Sunday, March 10th, 2019 (
No comments yet)
Sunday, March 10th, 2019 (
No comments yet)
Now the terrorist watch list is making it to our everyday lives.

Private businesses such as rental and mortgage companies and car dealers are checking the names of customers against a list of suspected terrorists and drug traffickers made publicly available by the Treasury Department, sometimes denying services to ordinary people whose names are similar to those on the list.
…
Yet anyone who does business with a person or group on the list risks penalties of up to $10 million and 10 to 30 years in prison, a powerful incentive for businesses to comply.
…
"It prohibits anyone from doing business with anyone who's on the list. It does not have a minimum dollar amount. . . . The local deli, if it sells a sandwich to someone whose name appears on the list, has violated the law."

This might be a good thing if it actually worked. Judging on how the no-fly list works, I'm guessing it doesn't.
So what happens when the terrorists start using names like:
- John Smith
- Mike Brown
- Chris Anderson
- Mary Jones
- Beth Miller
Tags:
Big Brother,
Big Business,
Treasury Department,
Watch Lists
Saturday, March 9th, 2019 (
No comments yet)
Not too long ago, a good friend of mine did a lot of work in understanding how copyright holders (such as those represented by the RIAA and MPAA for example) act and react to Peer 2 Peer filesharing networks.
I managed to dig up his 20 page essay on the topic which provides an in-depth summary of the P2P issue including suggestions on how to avoid being identified on a P2P network.
This is a great resource for someone who needs historical information on the issue or who is interested in building a secure P2P app. Also see my article on avoiding P2P nightmares for parents for additional tips and tricks.
Tags:
File Sharing,
MPAA,
P2P,
RIAA
Saturday, March 9th, 2019 (
No comments yet)
Wisconsin may have refused to help the RIAA, but the U of N actually took it all the way:

If there were any doubt that the university is really irritated by the RIAA's requests, it has requested that the RIAA pay the university to reimburse its expenses from dealing with this

That's so awesome 😀
Tags:
Big Business,
Bully Lawsuits,
RIAA,
Schools,
University of Wisconsin
Friday, March 8th, 2019 (
No comments yet)
According to the Washington Post, the FBI issued thousands of national security letters many without any clear ties to "emergencies" or current investigations.

Referring to the exigent circumstance letters, Sen. Charles E. Grassley (R-Iowa) wrote in a letter Friday to Justice Department Inspector General Glenn A. Fine: "It is . . . difficult to imagine why there should not have been swift and severe consequences for anyone who knowingly signed . . . a letter containing false statements. Anyone at the FBI who knew about that kind of wrongdoing had an obligation to put a stop to it and report it immediately."

No kidding. What I don't get is why everyone is saying that the "FBI's use of the exigency letters "circumvented" the law" rather than just say "They broke the law and many of the buggers are going to jail".
Tags:
Big Brother,
FBI,
George Bush
Friday, March 8th, 2019 (
No comments yet)
In my last experience buying a car, they tried to take my Social Security Number even though I had financing from someone else. I fought them for a half hour and nearly left the place until a manager got involved and saw the writing on the wall.
Now, it's getting worse. Public Citizen's blog points to an article about a car dealership that data-brokerings customers for their thumbprints before selling them a car. First seen at banks, the practice seems to be spreading.
Tags:
Big Business,
Thumbprints
Friday, March 8th, 2019 (
No comments yet)
In the RIAA's ongiong bully-lawsuit campaign, it has sent "settlement" letters to numerous Universities to be distributed to "alleged" abusers. The University of Wisconsin has refused to do so without a subpoena. Innocent before guilty? Wow. Count on a University to remember our Constitution.
Tags:
P2P,
RIAA,
University of Wisconsin
Friday, March 8th, 2019 (
No comments yet)
This article talks about a company who designs workplace monitoring software. This isn't new technology, but the reason I point it out is how human they make these guys seem. Check out the Star Wars and Battlestar Galactica references 😀
Tags:
Big Business
Friday, March 8th, 2019 (
No comments yet)
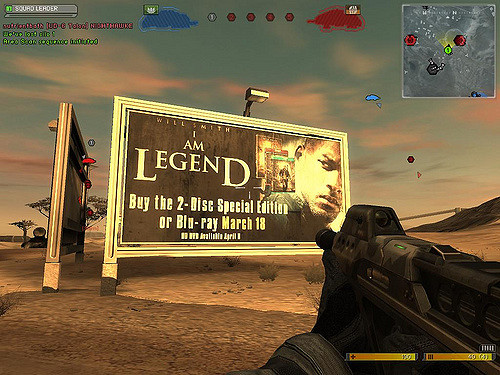
Now that Google is getting in the game (so-to-speak), the chance of seeing in-game advertising has just skyrocketed. Would a company like Google who tracks your searches match your ads to your search habits? Hmm…I guess Penny Arcade was right.
Tags:
Big Business,
Gaming
Friday, March 8th, 2019 (
No comments yet)







 Private businesses such as rental and mortgage companies and car dealers are checking the names of customers against a list of suspected terrorists and drug traffickers made publicly available by the Treasury Department, sometimes denying services to ordinary people whose names are similar to those on the list.
Private businesses such as rental and mortgage companies and car dealers are checking the names of customers against a list of suspected terrorists and drug traffickers made publicly available by the Treasury Department, sometimes denying services to ordinary people whose names are similar to those on the list.