Sunday, March 10th, 2019 (
No comments yet)
Now the terrorist watch list is making it to our everyday lives.

Private businesses such as rental and mortgage companies and car dealers are checking the names of customers against a list of suspected terrorists and drug traffickers made publicly available by the Treasury Department, sometimes denying services to ordinary people whose names are similar to those on the list.
…
Yet anyone who does business with a person or group on the list risks penalties of up to $10 million and 10 to 30 years in prison, a powerful incentive for businesses to comply.
…
"It prohibits anyone from doing business with anyone who's on the list. It does not have a minimum dollar amount. . . . The local deli, if it sells a sandwich to someone whose name appears on the list, has violated the law."

This might be a good thing if it actually worked. Judging on how the no-fly list works, I'm guessing it doesn't.
So what happens when the terrorists start using names like:
- John Smith
- Mike Brown
- Chris Anderson
- Mary Jones
- Beth Miller
Tags:
Big Brother,
Big Business,
Treasury Department,
Watch Lists
Saturday, March 9th, 2019 (
No comments yet)
Here's a fairly good checklist for what to do if you're a victim of identity theft.
The only problem is that he didn't mention the most effective tool for preventing ID theft that there is: Credit Security Freezes.
If you live in a state that has a freeze law, don't wait until you're a victim, do it now!
Tags:
Credit Freezes,
Identity Theft
Saturday, March 9th, 2019 (
No comments yet)
This story is hilarious! In short:
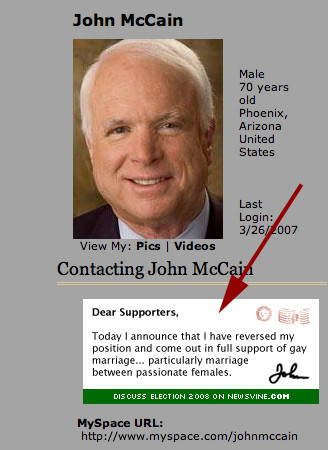
- John McCain, Senator and Presidential hopeful, set up a Myspace page to "connect with younger audiences"
- He used a default theme created by the author of this prank
- He not only didn't credit the author of the theme, but one of the images in the theme was being pulled from the author's webservers costing him money every time someone loaded McCain's page.
- The Author, to teach him a lesson, changed the picture to a joke political message
Anyway, read the details for a much better description by the author himself.
Tags:
Congress,
Image Hotlinking,
Internet Technology,
John McCain,
Justice Served
Saturday, March 9th, 2019 (
No comments yet)
In a disturbing, yet reassuring article, we find out that some sheep have been created that grow some human organs. The idea is to use them for organ harvesting which is sad and terrible, but better than the alternatives.
The first thing I thought of after reading this line was the movie "The Island" (which I just watched this week).

The process would involve extracting stem cells from the donor's bone marrow and injecting them into the peritoneum of a sheep's foetus. When the lamb is born, two months later, it would have a liver, heart, lungs and brain that are partly human and available for transplant.

Perhaps the stories of exuberant human harvesting will end. And hopefully, we won't have a future where our custom clones are raised and then killed secretly in an old underground military bunker.
Tags:
Futurism
Saturday, March 9th, 2019 (
No comments yet)
Not too long ago, a good friend of mine did a lot of work in understanding how copyright holders (such as those represented by the RIAA and MPAA for example) act and react to Peer 2 Peer filesharing networks.
I managed to dig up his 20 page essay on the topic which provides an in-depth summary of the P2P issue including suggestions on how to avoid being identified on a P2P network.
This is a great resource for someone who needs historical information on the issue or who is interested in building a secure P2P app. Also see my article on avoiding P2P nightmares for parents for additional tips and tricks.
Tags:
File Sharing,
MPAA,
P2P,
RIAA
Saturday, March 9th, 2019 (
No comments yet)
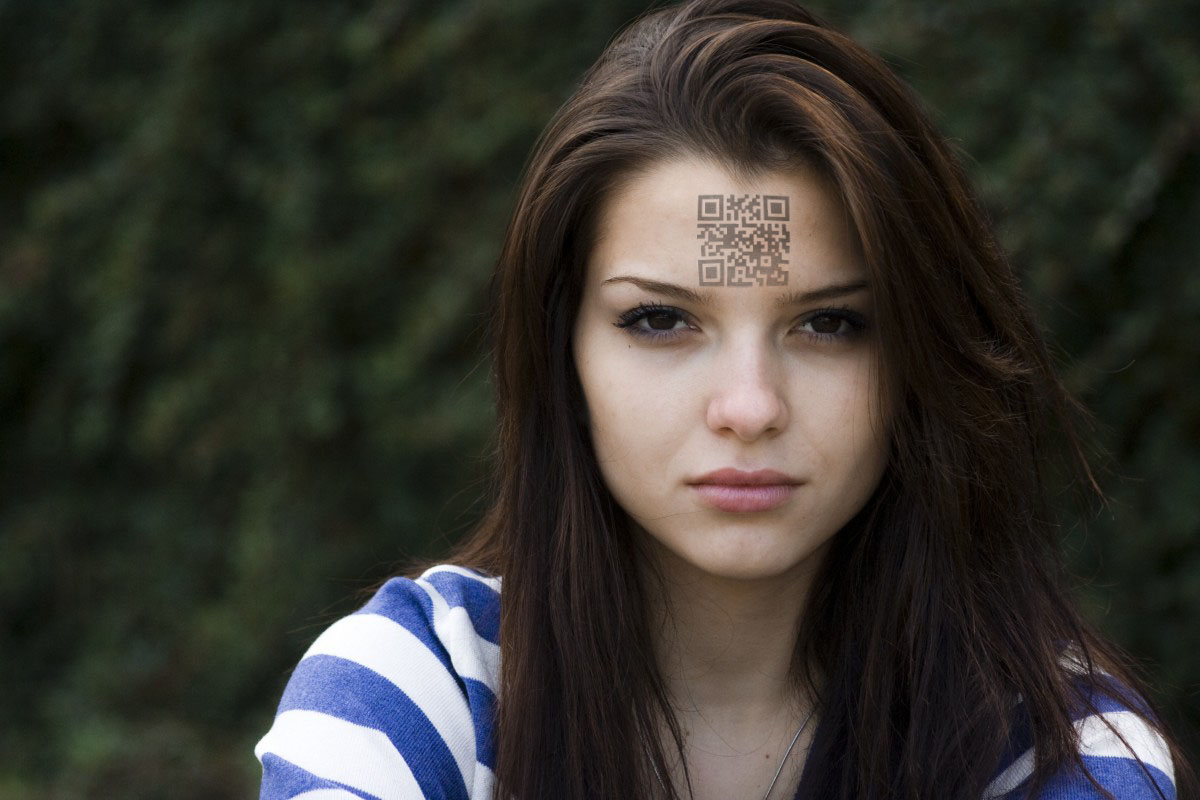
In an act of supreme stupidity and ignorance, Washington state has passed a law allowing residents to purchase an "alternative" drivers license that could be used in lieu of a passport at the Canadian border.

Citing the 9/11 Commission's support for more secure documentation for U.S. entry, Chertoff pointed out that U.S. Customs and Border Protection agents currently must look at more than 8,000 different forms of identification, whether birth certificates, driver's licenses or other documents.

So their answer to the problem?

The alternative license will contain a Radio Frequency Identification chip, commonly known as RFID, which the guard booths will use to scan the license as a traveler or trucker pulls up to the booth. U.S. passports issued since late 2006 already contain RFID chips.

They're going to offer a license that has no shielded covers like passports do that border guards will now just non-chalantly swipe across a reader rather than take the time to inspect. Brilliant. Maybe next, they can just put the readers out for the people in the vehicle to use making it even more convenient. That way, the criminals wouldn't have to bother changing the photo on the ID since no one would be looking anyway.
Tags:
Big Brother,
RFID,
State ID,
Washington State
Saturday, March 9th, 2019 (
No comments yet)
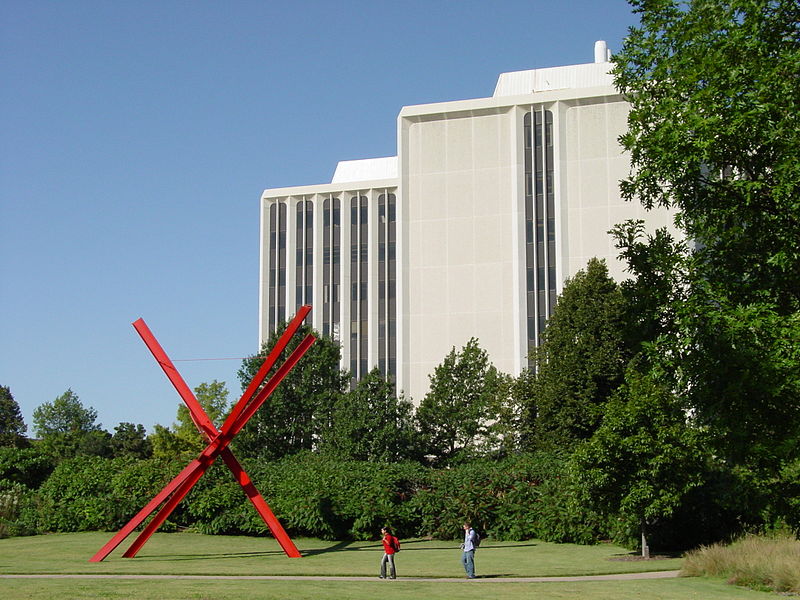
In the continuing saga, the U of N is now planning to charge the RIAA $11 for each threatening e-mail sent.

"We're spending taxpayer dollars tracking down RIAA problems," Weir said. "Are we an agent of the RIAA? Why aren't they paying us for this?"

And their response:

In response to NU's request, the RIAA's Engebretsen said, "It is neither practical nor appropriate for us to entertain a reimbursement request."

Tags:
Bully Lawsuits,
RIAA,
University of Nebraska
Saturday, March 9th, 2019 (
No comments yet)
What good would RFID passports be anyway if they don't work on security of issuance first? This article says that a suspected 10,000 passports were issued based on fake applications. That means that they have fully functional, non-cloned, non-hacked passports.
Tags:
Passport
Saturday, March 9th, 2019 (
No comments yet)
Senator Barak Obama, not to be outdone by Hillary, has posted some questions to Yahoo Answers.
Technically, Hillary has been on Yahoo Answers since last fall, but she's only asked three questions
Hillary's Questions
For the two older questions, it's interesting to see what answers she chose as the best. (note to track her questions,
click here for her profile).
- How can we help to prevent and someday eradicate breast cancer, which has touched the lives of so many people?
- Based on your own family's experience, what do you think we should do to improve health care in America?
- How can we as a country promote alternative energy, use less foreign oil and reduce global warming?
Barack's Question
His specific question, which I find far more useful than Hillary's so far, was "How can we engage more people in the democratic process?" I hope he reads my answer.
(Barack's profile here).
Tags: Barack Obama, Congress, Yahoo Answers
Saturday, March 9th, 2019 (
No comments yet)
Wisconsin may have refused to help the RIAA, but the U of N actually took it all the way:

If there were any doubt that the university is really irritated by the RIAA's requests, it has requested that the RIAA pay the university to reimburse its expenses from dealing with this

That's so awesome 😀
Tags:
Big Business,
Bully Lawsuits,
RIAA,
Schools,
University of Wisconsin

 Private businesses such as rental and mortgage companies and car dealers are checking the names of customers against a list of suspected terrorists and drug traffickers made publicly available by the Treasury Department, sometimes denying services to ordinary people whose names are similar to those on the list.
Private businesses such as rental and mortgage companies and car dealers are checking the names of customers against a list of suspected terrorists and drug traffickers made publicly available by the Treasury Department, sometimes denying services to ordinary people whose names are similar to those on the list.