Monday, March 4th, 2019 (
No comments yet)
Read about it here.
The question is, what will happen now that it's being monitored by the court that should have been monitoring it in the first place? Why is Bush allowing this? It can only be because he thinks they won't do anything about it.
Tags:
Big Brother,
George Bush,
Warantless Wiretapping
Sunday, March 3rd, 2019 (
No comments yet)
Sixwise gives and in-depth review of Best Buy's plan to "actively…eliminate " what they call "devil" customers. I've written about this before, but I like how they list specific actions that could land you on the "blacklist".
Most notably, this is the advent of "customer reports" similar to credit reports where you will be assigned a number based on profitability and treated accordingly. If you don't want to see that happen, make sure you let your legislation know.
Tags:
Angels and Demons,
Big Brother,
Market Lies
Monday, March 4th, 2019 (
No comments yet)
Here's a snippet from Ars Technica about how it's not just the FBI abusing power these days. From the article:
 Wired
Wired's Ryan Singel
adds a bit more to the story with the tidbit that the Pentagon plans to hang on to the records and feed them into TALON, the database project that the military uses for the data-mining part of its anti-terrorism efforts. Great! This is especially encouraging in light of the comments of Pentagon officials quoted by the
Times who claim that these records are typically used to knock names off of the suspects list. In other words, they look at the records, determine that Mr. Smith is completely innocent, has no ties to terror, and got his money legitimately, then they promptly feed his data into an anti-terror database.

Tags:
Big Brother,
CIA,
Pentagon
Sunday, March 3rd, 2019 (
No comments yet)
EPIC reports that the Department of Homeland Security is creating a passport-like system that will be required for travelers between the US, Canada, Mexico, the Caribbean, and Bermuda. This "passport" will contain RFID and very little security. From the article:

The federal government has been increasingly using RFID technology in its identification documents. The Department of Homeland security last year began using RFID-enabled I-94 forms in its United States Visitor and Immigrant Status Indicator Technology ("US-VISIT ") program to track the entry and exit of visitors.
19 This year, the State Department began issuing RFID-enabled passports to U.S. citizens.
20 Only 23% of U.S. citizens have passports.
21 Therefore, under the Western Hemisphere Travel Initiative, U.S. citizens would have to carry either a passport, which costs $97 for first-time applicants, or a PASS card. As the proposed Western Hemisphere Travel Initiative PASS card, U.S. passport, and US-VISIT I-94 entry and exit forms all contain RFID chips, if the PASS card proposal is adopted, then all U.S. citizens carrying either a passport or PASS card and visitors entering the country through US-VISIT will be able to be tracked using RFID technology.

Tags:
Big Brother,
Passports,
RFID
Sunday, March 3rd, 2019 (
No comments yet)
CNN posted an article about tiny transmitters embedded in some Canadian coins and planted on contractors with security clearance. From the article:

In a U.S. government warning high on the creepiness scale, the Defense Department cautioned its American contractors over what it described as a new espionage threat: Canadian coins with tiny radio frequency transmitters hidden insidee. Experts were astonished about the disclosure and the novel tracking technique...

Okaaaaay…. So, this is "creepy", and "novel"? First of all, coins can be given away very easily thus defeating the point of tracking the recipient. Second, the metal of the coin will inhibit the transmitters. Third, tracking technology already exists and is being used now. It's called rfid and it's already being put into our merchandise and even our clothes. Basically, it's much worse than coins.
Tags:
Big Brother,
Canada,
RFID
Sunday, March 3rd, 2019 (
No comments yet)
Schneier reports on a murder that was captured on a city camera system. He clearly thinks that such systems are pointless though the article seems to present it as being good (it caught a thief after all).
By using the worst possible scenario, however unlikely, it becomes easy to scare people into supporting something you personally want. When it comes to camera systems everywhere, remember this: absolute security can be acheived through absolute surveillance. This is true, but absolute surveillance also brings zero privacy and freedom.
Tags:
Big Brother,
Camera Surveillance,
Cameras
Sunday, March 3rd, 2019 (
No comments yet)
The EFF (who is also the organization spearheading the lawsuits against AT&T) is now taking on the secret profiling program that has hit the news recently. From their e-newsletter:

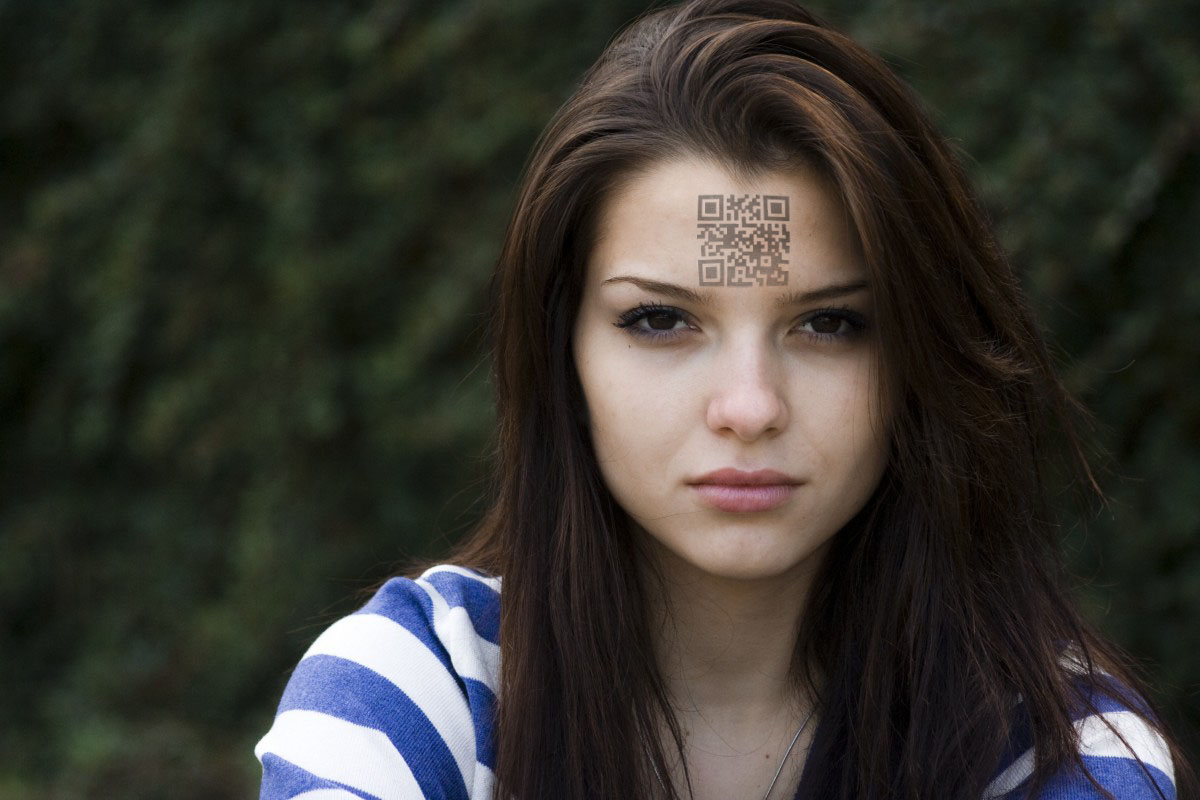
The Automated Targeting System (ATS) creates and assigns "risk assessments" to tens of millions of citizens as they enter and leave the country. In November, DHS announced that the program would launch on December 4, but Homeland Security Secretary Michael Chertoff later admitted that the program had already been in operation for several years.


Under ATS, individuals have no way to access information about their "risk assessment" scores or to correct any false information about them. But while you cannot see your score, it will be made readily available to untold numbers of federal, state, local, and foreign agencies. The government will retain the data for 40 years.

Tags:
ATS,
Big Brother,
Citizen Profiling,
Homeland Security
Sunday, March 3rd, 2019 (
No comments yet)
In this article, they explain that the Government can use the laws the way they're written now to read any e-mail that is hosted on someone else's computer (like the servers at AOL, Google, Hotmail).
A man who was partially convicted based on his e-mails is suing saying that it's unconstitutional for them to read his e-mails without a warrant. While the case is in appeals, the arguments are that e-mail should have the same privacy protections as snail mail while the government cites several reasons why they can and should be able to read them.
Tags:
Big Brother,
Email
Sunday, March 3rd, 2019 (
No comments yet)
cNet writes:

WASHINGTON–U.S. Department of Homeland Security Secretary Michael Chertoff on Thursday defended forthcoming national ID cards as vital for security and consistent with privacy rights.

From the article:

"Do you think your privacy is better protected if someone can walk around with phony docs with your name and your Social Security number, or is your privacy better protected if you have the confidence that the identification relied upon is in fact reliable and uniquely tied to a single individual?" Chertoff asked rhetorically.

Has anyone heard of false dilemma before? This is where you are presented with two choices when there are actually many. One choice is always extremely horrible to make the other seem reasonable. An example could be, "Would you rather put RFID in your credit cards or have a horde of violent viking warriors destroy your home and burn your family?"
 |  | False Dilemma choices are sometimes used accidentally, but are often a dirty trick to force people into agreeing or looking bad. Defeating them is only a matter of recognizing them when they're used and calling them out. |
Bottom line, do I have much trust that the government who brought us the RFID passport disaster and broken e-voting will get it right this time? No… no I don't.
Tags:
Big Brother,
RFID
Saturday, March 2nd, 2019 (
No comments yet)
In Schneier's blog today, he writes about a University of Washington study explaining how to track people using their Nike+iPod Sport Kit (which uses RFID).

This is a great demonstration for anyone who is skeptical that RFID chips can be used to track people. It's a good example because the chips have no personal identifying information, yet can still be used to track people. As long as the chips have unique IDs, those IDs can be used for surveillance.

Schneier goes on to say:

To me, the real significance of this work is how easy it was. The people who designed the Nike/iPod system put zero thought into security and privacy issues. Unless we enact some sort of broad law requiring companies to add security into these sorts of systems, companies will continue to produce devices that erode our privacy through new technologies. Not on purpose, not because they're evil -- just because it's easier to ignore the externality than to worry about it.

Couldn't have said it better myself.
Tags:
Big Brother,
Bruce Schneier,
Nike,
RFID








 Wired's Ryan Singel
Wired's Ryan Singel