Today at the Computers, Freedom and Privacy Conference, we opened with statements from representatives from the Obama and McCain campaigns (Clinton declined to attend).
Obama
Daniel Weitzner from MIT represented Obama's campaign. He opened by talking about Obama's major views as they relate to privacy and technology.
Obama believes in:
- Greater accountability in government
- Keeping government information and operations open and transparent
- Citizen participation in decision making
- The appointment of a government Chief Technology Officer to oversee these types of issues
McCain
Chuck Fish, a Patent Lawyer and part of McCain's legal team came to represent his campaign.
McCain believes in:
- Promoting American innovation
- Taxing the rich is a popular idea, but it's the pursuit of riches that drives innovation
- The system should reward the behaviors that we want to reward
- We need to develop a skilled workforce
- We should very lightly regulate the market and let it take care of itself until such point as they fail
- Market regulation should focus on anti-competitive behavior
Open Questions
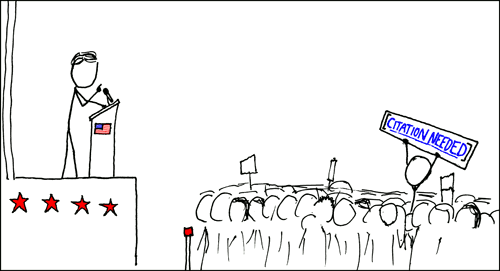
Next were questions asked by the moderators of the panel:
Q: "What do you see as the role of government in providing access to our basic communications infrastructure (the Internet)"
(McCain) Chuck – Can't understand his answer. Very politicalese. I'm fairly certain that he didn't answer the question, but it's hard to tell.
(Obama) Dan – Rather than focus on the infrastructure, it's important to protect the openness of the Internet. Even if we were to stay on dial-up or were years behind other countries on bringing broadband to our people, that's really secondary to protecting the nature of the Internet. He also noted that McCain's view of a self-regulating market will maintain open Internet (and I agree).
Q: "NSA Wiretapping – what would their position be on liability of carriers. What changes to Fisa"
(McCain) Chuck – "Immunity is a tough question because there's competing values. We're not talking about granting indulgences…" Again, hard to follow. Many words come out, but not much is said. The only thing he said of substance in his several minute non-answer to the question was "There needs to be hearings to find out what actually happened and what harm was actually done" which is to say that he will "look into it".
(Obama) Daniel – Obama's history and future view is to strengthen judicial review of administrative subpeonas, National Security Letters and the gag orders that accompany them. When surveillance is used, there must be real, meaningful oversight. Obama voted AGAINST retroactive immunity. McCain did not vote against them (which Dan feels is tacit approval).
Obama realizes that advanced surveillance and data mining can be important tools for national security, and they should be available, but with appropriate oversight. It's important to guard against mission creep! Woo! Someone gets it!
Q: "American companies are assisting China in censoring it's citizens. What would a given candiate do about that?"
(Obama) Dan – No official position, but if Dan had to offer advice to the campain, it would be that the lesson of the efforts in the US in the mid-90's to persuade countries to adopt an open Internet should be continued. We should open a dialogue and encourage and persuade countries to realize the benefits while using our influence to lead them towards more openness.
(McCain) Chuck – No explicit policy either. But the values that the campaign holds that would apply is to go slowly and carefully. It's always wrong to believe that you can legislate the behavior of people in other countries. Show the repressive regimes the benefits that openness provides, we will lead by example.
Open Questions
Next were open questions from the audience.
Q: "Email use by President – Will your candidate use e-mail. Does McCain know how? Will they avoid requirements to save e-mails by using other services outside of the Whitehouse?"
(McCain) Chuck – McCain does know how to use e-mail. As for avoiding requirements, you can tell from the tenor of his career that any perceived impropriety is anathema. Very little is more important for himself and country than acting honorably and keeping himself clean.
(Obama) Dan – There's a real commitment in Obama tech policy to keep government open and keep the flow of information open. Hiding e-mail wouldn't meet his commitment to open government.
Q: "Bush doesn't want to use e-mail because it becomes public record, but both of these candidates have records of believing in open government. But what will they do to keep government open?"
(McCain) Chuck – Answered by listing the example of require reporting of all data about sex offenders. He seems to have misunderstood that open government is about reporting what the GOVERNMENT is doing, not citizens.
(Obama) Dan – Bush administration has gone way overboard in classifying information. Obama called for national declassification center.
Q: "Clinton administration mandate cell companies to track users for 911. Companies are tracking all the time when powered. No legal limitations for what use can be made. Should this be protected by judicial oversight?"
(Obama) Dan – No position on that, but clear position of looking at tech capabilities that are not being addressed from a privacy perspective.
(McCain) Chuck – First ask, is there a problem and does the law already deal with it? If there was a possibility of current harm or future harm, then perhaps regulation would be appropriate, but otherwise, just trust but verify.
Q: "Net Nuetrality – How far would either of you go to live up to the view that the Internet is a tool for Democracy?"
(Obama) Dan – Obama wants to maintain openness of the Internet. Before we fight what the Internet may become, we should ask if we want to go where it's going. Do we like what it's evolving too. Either way, currently the regulatory agencies lack the power to get involved.
(McCain) Chuck – Understand Internet is important. But adverse to regulation, must have real evidence of harm. Don't want to stifle innovation.
Q: "Where do you think the burden lies for protecting information. American's must show harm? Or burden on Government that there's a justification for accessing my private information"
(McCain) Chuck – Companies always have known more about us than the government. We shouldn't have solutions seeking problems, but the opposite. Show the problem before acting.
(Obama) Dan – Increase FTC enforcement authority and budget. Too much burden on individuals to negotiate their privacy rights with whoever they deal with. Though our privacy laws are more modest than others, we've seen progress in our regulation. It's not up to normal people to protect their personal security. That's unreasonable. We don't have the time, energy, or (sometimes) capability.
Q: [my question] "Does your candidate realize the problem of Congress creating laws that over-rule stronger state laws that protect our privacy and freedom and would they have the balls to veto such a law?"
(McCain) Chuck – Clearly recognizes the importance of federalism. Always the rub whether what you have is well intentioned preemption or something else. Not the campaign's policy to over-turn what approaches of 3 centuries of preemption law. In other words, leave it to congress to make the determination of what is an appropriate level of preemption.
(Obama) Dan – No general position on preemption, but it's a right thing to keep an eye on. In other areas the benefit of some mount of federalism, but preemptive will come up. Depends on context.
Summary
This affirms in my mind that Obama is far beyond McCain in understanding privacy and technology issues. Obama wants to undo some of the damage Bush has done to us in recent years and is aware that regulatory agencies are valuable. He even believes in passing laws BEFORE there's a critical breakdown.
McCain is a fool that believes the market can regulate itself.
Tags:
CFP








 As part of a social experiment, attendees at a hacker conference in July will be issued badges with electronic tracking devices. Large displays will show in real-time where people go, with whom they associate, for how long and how often.
As part of a social experiment, attendees at a hacker conference in July will be issued badges with electronic tracking devices. Large displays will show in real-time where people go, with whom they associate, for how long and how often.