From Dead to Diamonds – Sure Beats an Urn


I've heard of this before: taking the remains of your loved ones and having them made into synthetic diamonds. I didn't know you could pick colors though.
.... [Click here to read the rest of this post]Tags: Diamonds, FuneralsFree Product Recall Information By E-mail, No Registration Required


Public Citizen reports that the Consumer Product Safety Commission has begun a service that will notify consumers by e-mail of any product safety recalls. While some manufacturers will do this voluntarily, some won't and even if they do, they usually ask for you to register all your products (including loads of personal information .... [Click here to read the rest of this post]
Tags: CPSC, Families, Product SafetyQuicken and MS Money Extort From Their Users

The Consumerist is running an article explaining how both Quicken and MS Money improperly and possibly illegally force users to upgrade to newer software by purposely cutting off necessary features to older versions.
.... [Click here to read the rest of this post]Tags: Customer Abuse, MS Money, Planned Obsolescence, QuickenPrivate Lenders Turn Away People on The Terrorist Watch List

Now the terrorist watch list is making it to our everyday lives.
 Private businesses such as rental and mortgage companies and car dealers are checking the names of customers against a list of suspected terrorists and drug traffickers made publicly available by the Treasury Department, sometimes denying services .... [Click here to read the rest of this post]
Private businesses such as rental and mortgage companies and car dealers are checking the names of customers against a list of suspected terrorists and drug traffickers made publicly available by the Treasury Department, sometimes denying services .... [Click here to read the rest of this post]24 Point Checklist for Identity Theft Victims – Good, But Missing the Most Important Step

Here's a fairly good checklist for what to do if you're a victim of identity theft.
The only problem is that he didn't mention the most effective tool for preventing ID theft that there is: Credit Security Freezes. If you live in a state that has a freeze law, don't wait until you're a victim, do it now!
.... [Click here to read the rest of this post]Tags: Credit Freezes, Identity TheftJohn McCain Stole Credit and Bandwidth, Paid Dearly
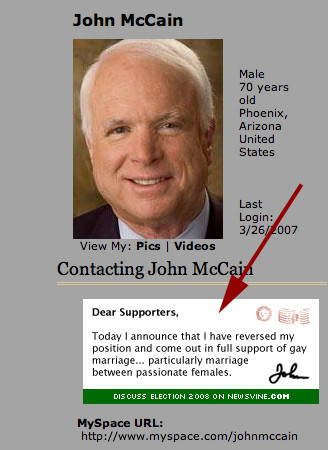
This story is hilarious! In short:
- John McCain, Senator and Presidential hopeful, set up a Myspace page to "connect with younger audiences"
- He used a default theme created by the author of this prank
- He not only didn't credit the author of the theme, but one of the images in the theme was being pulled from the author's .... [Click here to read the rest of this post]
15% Human Sheep For Organ Harvesting


In a disturbing, yet reassuring article, we find out that some sheep have been created that grow some human organs. The idea is to use them for organ harvesting which is sad and terrible, but better than the alternatives.
The first thing I thought of after reading this line was the movie "The Island" (which I just watched .... [Click here to read the rest of this post]
Tags: FuturismDetection Methods Used by Copyright Holders

Not too long ago, a good friend of mine did a lot of work in understanding how copyright holders (such as those represented by the RIAA and MPAA for example) act and react to Peer 2 Peer filesharing networks.
I managed to dig up his 20 page essay on .... [Click here to read the rest of this post]
Tags: File Sharing, MPAA, P2P, RIAAWashington State Dumb as Dirt – Uses RFID in Licenses
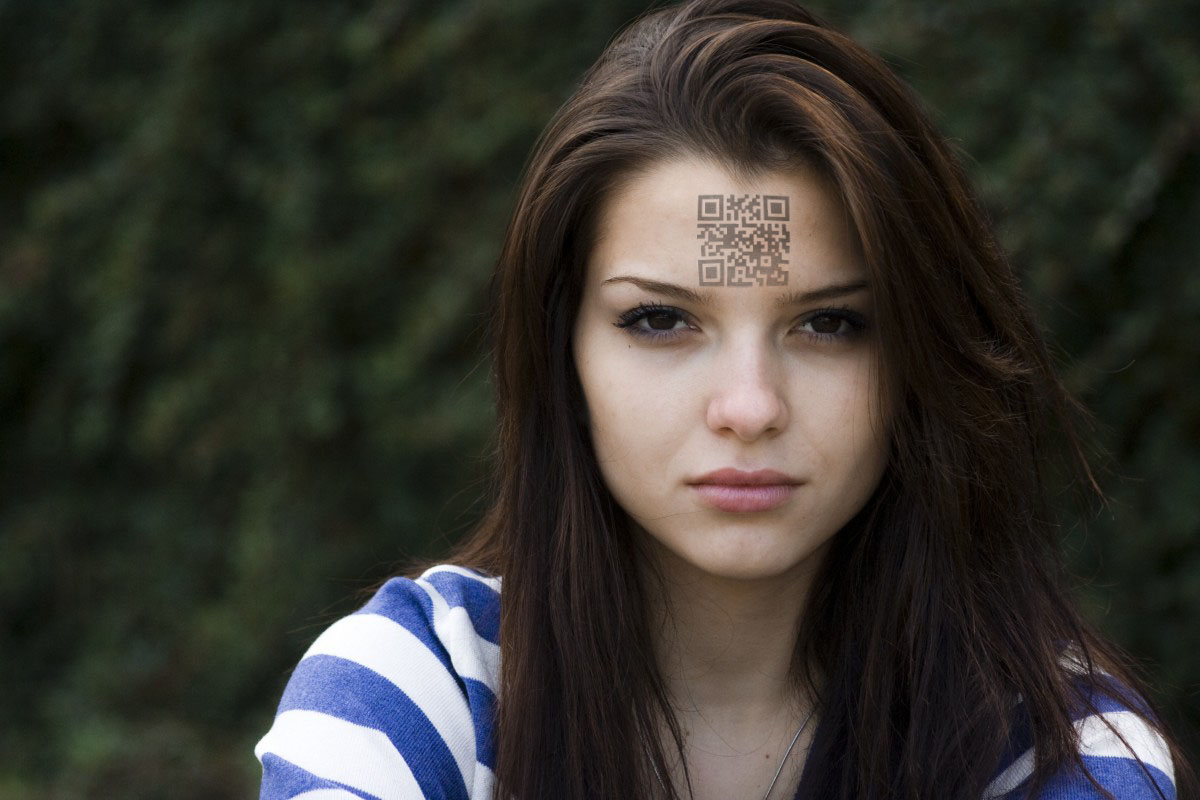
In an act of supreme stupidity and ignorance, Washington state has passed a law allowing residents to purchase an "alternative" drivers license that could be used in lieu of a passport at the Canadian border.
 Citing the 9/11 Commission's support for more secure documentation for U.S. entry, Chertoff pointed out that U.S. Customs and Border .... [Click here to read the rest of this post]
Citing the 9/11 Commission's support for more secure documentation for U.S. entry, Chertoff pointed out that U.S. Customs and Border .... [Click here to read the rest of this post]University of Nebraska – Continues to Insult the RIAA

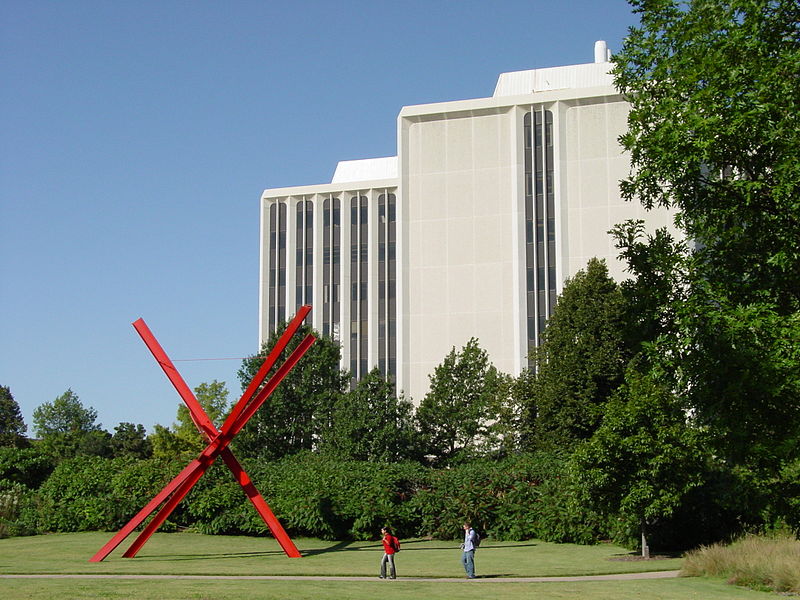
In the continuing saga, the U of N is now planning to charge the RIAA $11 for each threatening e-mail sent.
 "We're spending taxpayer dollars tracking down RIAA problems," Weir said. "Are we an agent of the RIAA? Why aren't they paying us for this?"
"We're spending taxpayer dollars tracking down RIAA problems," Weir said. "Are we an agent of the RIAA? Why aren't they paying us for this?"
And their response:
Tags: Bully Lawsuits, RIAA, University of Nebraska





