Saturday, January 19th, 2019 (
No comments yet)
An RFID tag is nothing more than a little chip attached to a paper-thin antenna. The chip's basic function is to store and transmit a small amount of information, usually just a unique identifier. What good is that? Well:
Pros
 |  | Though there hundreds of visionary and useful things you can do RFID, because they typically lack strong security controls there are serious risks that come with them too! |
Cons
Making RFID Safe
RFID, like most technology, isn't something that can (or necessarily should) be stopped. Intstead, we need to harness and direct the technology to reduce the threat. To do this, we need to look at three risk aspects of RFID:
1. Poor authentication
One of the primary issues with RFID and the main thing that makes all the nightmare scenarios possible is that unsecured RFID broadcasts to anyone and everyone. For any implementation of RFID to be acceptable, the chips must be programmed only to speak to proper readers who authenticated themselves first.
For example, say you have a refrigerator that scans the food inside. When you put food inside, the fridge should program the food with a one-time code that makes it impossible for the chips in the packaging to respond to any other reader.
 |  | Think no one cares what the contents of your fridge are? Think again. |
2. Poor (or no) encryption
Even after a chip authenticates a reader, if it sends the data out in the open, anyone else nearby (or not so nearby) can read it too. All communications between a chip and authenticated reader must be encrypted to prevent eavesdropping by others.
3. Use of Long-term RFID
Implantation is permanent. Passports are good for 10 years. Companies plan to replace UPC barcodes with RFID that will transmit ID codes for the life of the product (from creation to landfill and beyond).
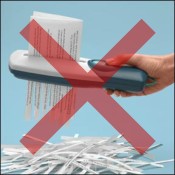
Every RFID implementations will eventually be hacked by someone. All it takes is one person in the world to find a way to break the system and the security is no good anymore (like the millions and millions of pounds wasted with the UK passports). Secure implementations can slow it down or help, but the best defense is NO RFID.
I can't see implants ever making sense and you definitely want to be sure the products you wear and carry around can't be used to wirelessly communicate with the world around them.
Tags:
Privacy,
RFID,
Security,
Spychips
Saturday, October 10th, 2009 (
No comments yet)
You may have noticed the lifecycle of e-mail accounts goes something like this:
- New – You worked hard to get a username that hadn't been taken. You've excited to share it with all the people you know.
- 1st Spam – Some jerkwad has defiled your account by sending you a random unwanted advertisement or Phishing e-mail. No big deal… it's just one after all.
- Tipping point – It's starting to get serious. You're getting more bogus e-mails every day than real.
- Abandonment – You've given up on the account. There seems to be no way to repair the damage and you're resigned to moving on. You create a new e-mail account and start the cycle over again.
The problem with this approach is that changing e-mail addresses can be extremely difficult. All your friends and family can probably be updated with the new address by sending them all a simple e-mail with the new address. But all those web stores and accounts you have will have to be updated manually. It can be done, but it's a chore. Worst case, you used this account for business and now you have to update all your customers which is not only a pain, but looks pretty unprofessional.
Creating a Decoy
The way this works is very simple, pick and use an e-mail account for your friends, family, business contacts, etc. Then go and make a DIFFERENT one perhaps the same one, but with a series of numbers after it.
Ex: butterbean@yahoo.com for your main account and butterbean100@yahoo.com for your buffer.
Now all you have to do is keep your main account safe by not giving it out to any websites or people you don't trust. For anyone you're not sure of or anyone you don't plan to do business with over a period of time (for example, making a single web purchase from a store online), provide the decoy.
Do your best to keep spam and other e-mail garbage out of both, but if eventually the decoy account gets buried and becomes useless, discard it and get another one (butterbean101@yahoo.com for example).
Monday, July 5th, 2010 (
No comments yet)
E-mail was the catalyst that turned a simple military communications effort into the monstrosity that is the Internet today. It turns out, people really like to communicate.
The problem is that there are many technical and social means by which bad guys can take advantage of you via your e-mail. Here I will present some some of the problems you will face and some tips for protecting yourself and others.
E-mail Dangers
| Until we find out who the people are who actually buy things from spammers and kick them off the Internet, you're going to have to learn how to deal with and prevent spam. |
| E-mail Viruses - Learn how viruses are spread through e-mail and how to stop them |
| Phishing - Spot and avoid lures that pull you into the dark side of the web |
| Don't be one of those people that loses thousands of dollars to the classic Nigerian Scam. |
E-mail Etiquette
| Use Reply-All when you mean to and never when you don't. |
E-mail Tips and Tricks
Tags:
E-mail,
Email,
Phishing,
Spam
Monday, July 5th, 2010 (
No comments yet)
If you were the lead on a project for a company and a vicious competitor happened to find out that you were a recovering alcoholic, what would happen if they waited until the wife and kids were out of town for the weekend and they left a wine sampler on your doorstep?
What if your neighbor secretly hated you for something they never bothered to tell you so they waited until you were on vacation and posted a prank ad in the paper that everything in your house was free for the taking.
You might be amazed at how much trouble you can cause for someone if you know enough about them. Think about the movies where a group of people face impossible odds to rescue hostages, rob a bank, or other fantastic feat. The only way they're able to pull it off is because they already know all the security, the layout of the buildings, the defensive measures etc.
Just like in the movies, the more someone knows about you, the easier it is for them to manipulate or destroy you. Don't let that happen! Learn that your information is important and it should be protected.
Saturday, March 5th, 2011 (
4 comments)
All of the following advice is based on the premise that you will only use it to protect your privacy and not to violate rules of ethics or legality.
What Is It?
What I call a privacy alias is a complete profile of your data: name, address, phone number, social security number, birthplace, etc… except all fake. Completely made up. False.
For example, I have real data. But it's nothing that I'll share with you or most other people without specific need (since I subscribe to The Geek Privacy Principle). The point is that you don't want to give people your real data is you can avoid it. But the problem is sometimes you don't have a choice but to give up information.
When to Use It
2497 Milford Street
Campton, NH 03223
| Website | BinocularDistributor.com |
| Email Address | DannyABlair@example.com |
| Password | ieC3ohPaz9 |
| Phone | 603-726-4397 |
| Mother's Maiden name | Pollak |
| Birthday | September 15, 1945 |
| Visa | 4916 1711 7909 3400 |
| Expires | 7/2011 |
| SSN | 732-00-5043 |
| Occupation | Prepress technician |
| UPS Tracking Number | 1Z 236 756 94 1867 824 3 |
You're not going to use some of this data like the Visa or the UPS number (those are for people who want to test web ordering systems), but the rest is a good start if you're having trouble thinking up your own data to use. The main issue is that the address, phone number and Social Security Number may belong to some real person.
If you want to be safe, use Fakenamegenerator.com for ideas, but use my technique instead:
Creating Fakes More Carefully
Instead of creating completely fake data that's harder to remember and more likely to match some other real person (which then makes YOU the problem for someone else), I recommend you use part of your real data for your privacy alias.
Fake Name
Because it's too confusing to use a fake first name (unless you're used to going by two different names), I tend to use my real first name. My alias last name can be based on your middle name, a nick-name, a pet's name, a famous person's name or anything else you want.
Fake Address
For the address, I chose a fun word (ex: crater) and decided that would be my street name. Then I just checked some cities on Google maps and tried to find a street with that name. When I found a city that did not have a street with that name, that was the one I chose.
Fake Phone

If they don't use it as they say, there's no harm

I'm often told that they "will never use my phone number to call me" so why not set them up for some retribution if it turns out they're lying? I tell them my number is 900-900-9000.
If they don't use it as they say, there's no harm. If they do call it, they'll be helped by a very friendly person who will happily charge them by the minute 🙂
Fake E-mail
You should already have multiple e-mail accounts for this purpose, but you feel obligated to provide an e-mail and you never want any communication from the asker, just make up whatever you want. You're more likely to avoid a real person's e-mail if you use null@anything.com. Null is a special work in networking that will never go to a real person's e-mail.
Fake Birthday
This one's pretty easy. Pick someone who's close to you or someone famous that you admire and use their day and month with your year.
Fake SSN
The trick I usually recommend is to use your real SSN with the middle two digits replaced by 0. There are three reasons for this:
- It's hard to remember a completely fake SSN
- If challenged in some way, it's easy to claim innocence and that it was entered wrong or a computer glitch led to the "error".
- You will never end up using someone else's SSN this way.
The one problem with Fakenamegenerator.com is that they don't make any efforts to create SSN's that don't already belong to someone else. They depend on the odds of the SSN not matching your fake name, but this method is safer because any all 0 field in an SSN automatically makes the number invalid in the system.
Fake Challenge Questions
As part of your profile, make sure you have answers for all the common challenge questions you'll see on websites like:
- What's your mother's maiden name?
- Where were you born?
- What was the brand of your first car?
- What was the name of your favorite pet?
Functionally speaking, this information is used to help you access your account if you forget a password. What what if someone who knows you uses it instead? Have you ever known someone who's account got hijacked?
Obama, Sarah Palin, Britney Spears, and others have all data brokers, almost anyone can get it too. It's just never smart to use real information so have some fake stuff prepared.
 |  | Even if you use the same fake information everywhere, that's better than using real data. However, even better than that is to use different data everywhere. If you do, be sure to store it securely so you don't forget it.. |
Summary
Once you've taken the trouble to make a fake profile, your goal is to use it forever (or as long as you can) so give it good protection. I store mine with my passwords in an encrypted file so if you don't have software to encrypt yet, maybe it's time you go get some.





















 If they don't use it as they say, there's no harm
If they don't use it as they say, there's no harm





