Sad News: Women Loses to RIAA in Court

The woman who was the first to successfully get a jury trial in a RIAA case lost. Even assuming they were able to prove that she had downloaded the files and left them in her share folder, the chances are she didn't know she was sharing what she downloaded and the RIAA has no way to prove actual damages, just .... [Click here to read the rest of this post]
Tags: Legal BullyingOnline Site for Scams Fraud Etc

If you're a privacy nut and have a health dose of paranoia, you'll like this new website designed by the New York Public Interest Research Group (NYPIRG): CyberStreetSmart.org. It's a nicely designed site with easy access to information on major types of online scams. Unlike the paltry efforts of some other organizations, this site is easy to navigate and keeps the .... [Click here to read the rest of this post]
Tags: Scam DefenseAccountability Office Report Shows FCC is Not Doing its Job

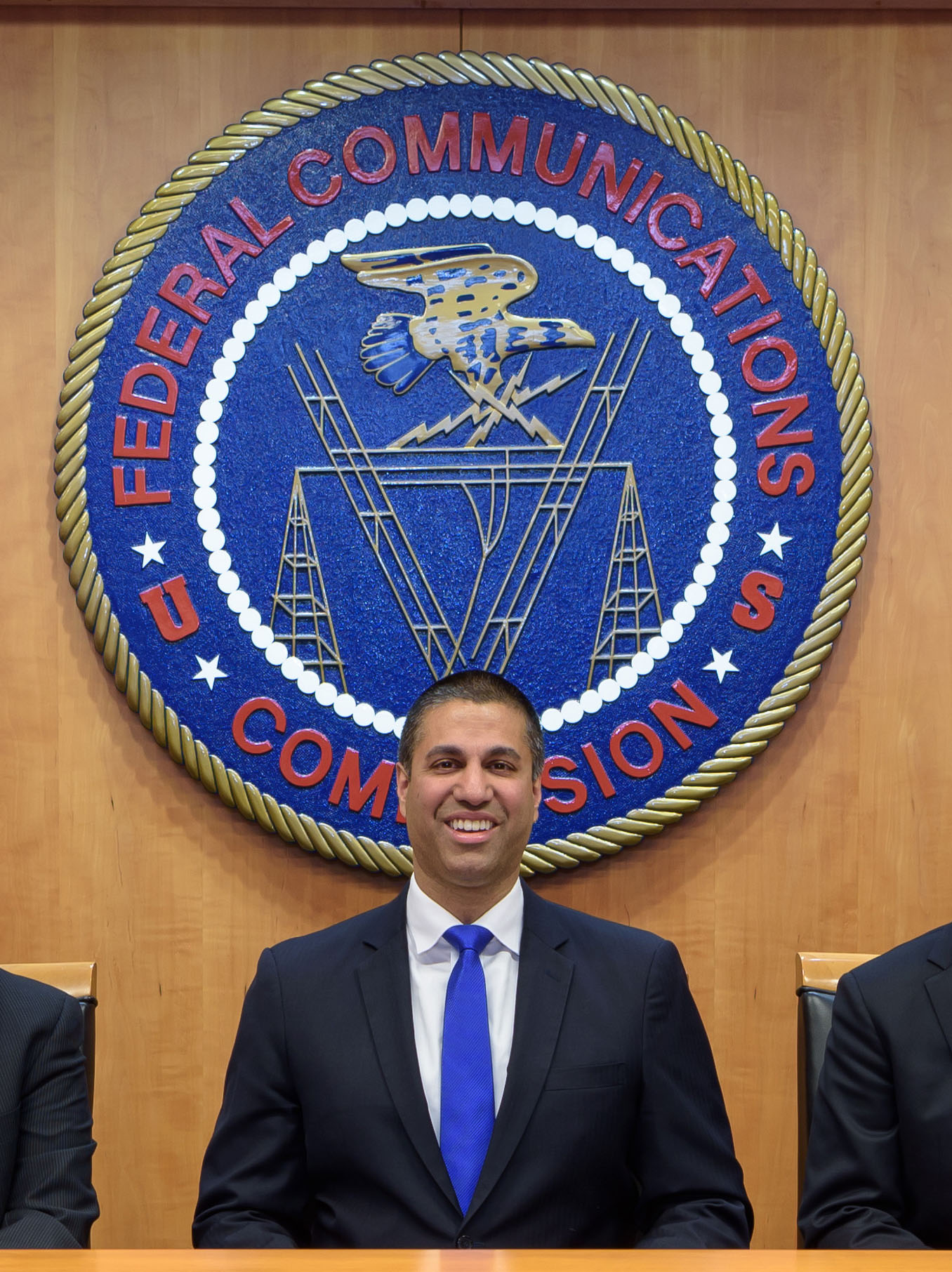
Sometimes it seems that the Government Accountability Office is the only one trying to do it's job. In their report on the Federal Communications Commission, they state that the agency favors lobbyists over citizens in that lobbyists are kept up to date on FCC actions while citizen groups were not.
Granted, they need to do .... [Click here to read the rest of this post]
Tags: Accountability, FCC, OversightConfessions of a College Credit Card Pusher (Wanna Free Shirt?)

If you've been on college campuses these days, you'll often see the booths where you get a free shirt or coffee mug for signing up for a credit card. Well, it's pretty obvious that college kids have no idea how to handle credit and the credit card companies know it.
 Rhoades took the job and .... [Click here to read the rest of this post]
Rhoades took the job and .... [Click here to read the rest of this post]Congress Finally Taking AT&T (etc.) to Task?

Now that Congress has officially started to investigate the role of major telcom companies in illegal spying, the question is, "will anything finally come of it?"
At this stage, they've only sent letters asking about their involvement and whether they knowingly broke the law under the promise of protection from litigation from the executive branch. If they actually .... [Click here to read the rest of this post]
Tags: Congress, George BushSummary of iPhone Woes

The iPhone was greatly anticipated as revolution in wireless phones (in some circles, it's been called the "Jesus phone"). As soon as it was released, hackers and tweakers got to work on unlocking it so it could work on other carriers or just be used as a PDA/MP3 player without phone service at all. Soon after that was .... [Click here to read the rest of this post]
Tags: Apple, iPhoneYou Can Get Viruses From Video Files, But You Shouldn’t

Even if a hacker put some code into a music file (for example), the music file player should just try to send the code to the speakers along with the rest of the data, not actually perform any commands (like taking over your computer). For this to be possible, the makers of the player software practically have to .... [Click here to read the rest of this post]
Tags: Media VirusWho is Ron Paul – Are You Sick of His Name Yet?

I see noise about "Ron Paul" everywhere. Streets, media, online. It's enough to get on your nerves. But as with all things popular, eventually, you want to see what the fuss is about.
I checked out his website today and if half of the things there are true, he might be our best presidential candidate in a long, .... [Click here to read the rest of this post]
Tags: Ron PaulSprint/Nextel Extended Customer Contracts Without Warning


Sprint used any minor changes to service plans to extend customer contracts by up to two years.
 “When you receive complaints across the board, from firefighters to lawyers, from retirees to construction workers, all of whom feel they were unfairly manipulated by their cell phone company, you have a problem, ? Attorney General Lori Swanson .... [Click here to read the rest of this post]
“When you receive complaints across the board, from firefighters to lawyers, from retirees to construction workers, all of whom feel they were unfairly manipulated by their cell phone company, you have a problem, ? Attorney General Lori Swanson .... [Click here to read the rest of this post]UK Police Can Demand that You Decrypt Information or Jail You


In the UK, ever the pinnacle of freedom and privacy, you can now be forced to decrypt any data that they believe has bearing on a criminal or terror investigation. Here's the really fun part (emphasis mine):
 Individuals who are believed to have the cryptographic keys necessary for such decryption will face up to .... [Click here to read the rest of this post]
Individuals who are believed to have the cryptographic keys necessary for such decryption will face up to .... [Click here to read the rest of this post]





